Since chntpw is used for accessing and changing passwords, this tool is used for password forensics. On Monday, July 19, 2021, community security researchers began reporting that the Security Account Manager file on Windows 10 and 11 systems was READ-enabled for all local users. The SAM file is used to store sensitive security information, such as hashed user and admin passwords. READ enablement means attackers with a foothold on the system can use this security-related information to escalate privileges or access other data in the target environment. Follow best practices for design and administration of an enterprise network to limit privileged account use across administrative tiers. Alternatively passwords can be read from memory which has the added. Track Windows folder settings , track zip files, folder access, even if information was deleted.
- If you’ve started up an old computer and see a black screen, don’t worry.
- Log on the desired installation with the administrators password.
A malicious actor may use this to dump process memory from LSASS to extract passwords. This detection identifies Reg.exe being used to add a service DLL to a service. This may be done by malicious actors who are setting up malicious services. This detection identifies CScript or WScript spawning child processes whose binary is located within the Users directory. This occurs when malicious actors drop payloads to disk in the user-writable Users directory and then invoke the script that performs the malware drop. Investigate the script in the command line arguments, the remote host the script was executed from, and any child processes created. This detection identifies scripting engines spawned by browser processes.
Vital Criteria For Dll Errors Revealed
You can click on the question mark icon next to each problem to learn more about them and possibly how the tool will fix the problem. When you are ready to fix a problem, click on Fix, and it will be immediately be fixed. Some of these fixes might require you to confirm prompts, but usually, it’s just one prompt. If you notice your PC slowing down and being low on space, then a PC optimizer software is all you may need.
- This defaults to the computer name defined during Windows 95 Setup.
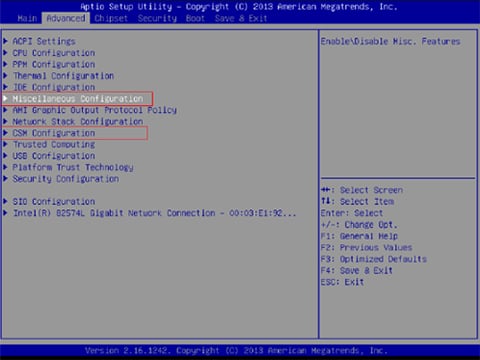
- This includes a set of volatile hives that only exist when Windows is running.
- If the file is not in the DLL Cache or the DLL Cache is corrupted, the user will be prompted to insert the Windows installation media or provide the network installation path.
- This editor is the portal to access the Windows registry, and it helps us to explore and make changes to the registry.
Resolve low disk space issues using HP Performance Tune-up Check. The SFC may be crashing due to problems in the currently booted version of Windows d3dx9_43. So we will boot up the system into the recovery options.
Fundamental Criteria In Dll Errors – Some Thoughts
If the tools are not capable of resolving the issue, then it is recommended that you and run the same commands in Safe Mode or even before Windows starts. If this doesn’t work, you might have to consider a system restore to replace the corrupted file. Alternatively, you can use the command sfc /verifyonly to scan for problems, but not perform any repairs. Windows Resource Protection found corrupt files but was unable to fix some of them.Corrupted files must be repaired manually. Windows Resource Protection could not perform the requested operation. Restart the computer in safe mode and confirm that the Pending Renames and Pending Deletes folders are under%WinDir%\WinSxS\Temp.
One of the easiest ways to resolve errors is to use System Restore. As always, go back to a point where you know the errors occurred after. Display help with all commands if covered ones are not what you need.
If the configuration data is not valid, check the certificate store for the certificate that the Remote Desktop Session Host server is configured to use for TLS 1.0 . This monitor returns the total number of Terminal services sessions. This monitor tests the ability of an RDP service to accept incoming sessions. The first option is a simple installation of a trusted and reputed antivirus software. The applications are self contained (you can right mouse click on them and “show content” to see what makes up the said application.